
There is no surprise that brands today need data to win against their competitors, they need data to be bigger than what they are in the market, and above all, they need data to prove their prospects that their brand has what it takes to sell to them.
Data is the most crucial asset any business can have especially in 2020 and the years to come “Data is a precious thing and will last longer than the systems themselves.” – By Tim Berners-Lee, Inventor of the World Wide Web
With data, a brand can achieve success in multiple ways such as with their prospects' data, they can capture the online behaviour of them and then curate advertisements on the basis of that. As a prospect, that is what they want to see and they will click on the brand’s ad.
However, as meaningful it sounds from the brand’s point of view, there are more risks attached here.
Did you know that there is something called **‘browser fingerprinting’ **and this process can reveal so much about you?
Now imagine what would happen if you were being tracked and your browser data is being captured from smart hackers?
While a brand captures information to learn about you, or the hacker trying to enter into your system, your information, or rather your online actions need to be secured.
Everyone has the right to share information only on the basis of getting it approved by themselves first, anything that an individual is unaware of their information being viewed is wrong.
You need to secure your online browsing actions and there is a way to get that done.
It’s time for you to be safe and we will guide you on the right path with this article.
Let’s get you secured.
Post Quick Links
Jump straight to the section of the post you want to read:
MEANING OF BROWSER FINGERPRINTING
Browser fingerprinting is the process of capturing your action with the browser you use. The information collected could be anything such as the browser type you use, operating system details such as screen resolution, time zones, plugins, and more.
The hackers can even go on to scrape more actions of yours with the browser such as which pages tap your attention the most, which pages you visit, and more. All of this tracking is done for a purpose as stated earlier.
Let’s understand this with an example:
From a brand point of view, if a brand captures all the above information, they can then get a better understanding of you, when this happens, they will start to create advertisements that will draw your attention towards them and you will go ahead and follow where that ad will take you.
While this can help the brand to learn better about their prospects, there is a flaw from the prospect end such as the seriousness of being tapped.
Interesting Read : 6 Best Browser Automation Tools for Web Scraping
Have you wondered how when you think of something such as say you searched on Google for ‘best perfume brands’ and then suddenly on Instagram you find an ad related to the perfume?
Don’t you feel a pinch of shock and fear that how is this happening?
This is exactly what is happening with your browser fingerprinting as well.
Your browser is the place where all your needs and queries have the chance to be resolved so imagine tracking it would lead to multiple of your information being shared.
Let’s dig in a bit deeper to understand how this fingerprinting tapping takes place.
TYPES OF WAYS ONLINE TRACKING IS TAKING PLACE FOR YOU
1 . COOKIES AND TRACKING
Have you realized how when you try to view a website the website will be designed to fit whether you view it in a laptop or your phone?
This happens because of cookies. Cookies are small text files that will be stored on your computer and the information will be shared so that the experience you will have with a website or page is better.
The tracking takes place multiple ways such as enhancing fonts, browsing history, and more. This can give away a lot of your information under the ideology of enhancing your experience.
2 . CANVAS FINGERPRINTING
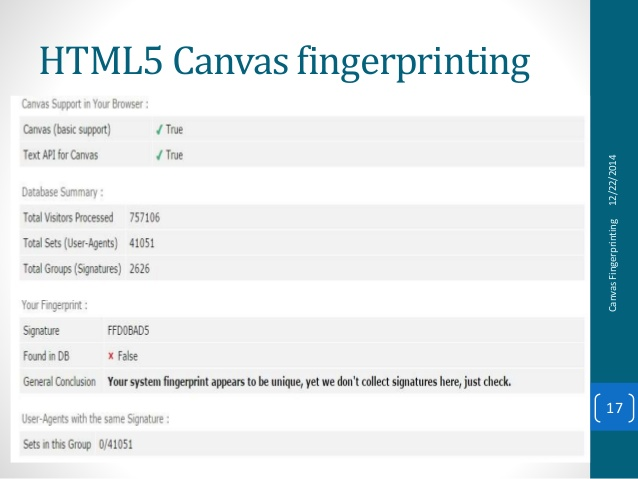
Canvas fingerprinting is another way to tap fingerprinting online. As you are aware that in order to write a website you require the HTML code 5, so inside that code there is another code listed which is the way the fingerprinting will be tapped.
The tapping happens when they use particular data such as text colour, the font size of the website browser. This is the information that will be used to understand the user.
3. IP ADDRESSES
An IP address is a unique code which every user has.
To access anything, the IP address will be displayed. When the other end of the receiver sees your IP address they will be aware of which location you are trying to view the information you want.
However now, IPs can also be tracked. It can reveal the accounts you logged in, your geolocation, and even the websites you often visit.
Now that you’re aware of the ways of how your fingerprinting is being tracked online, it’s time to reveal the solutions that can help you escape the trap.
PREVENTIVE MEASURES THAT WILL SECURE YOUR ONLINE ACTIONS
1 . GO INCOGNITO
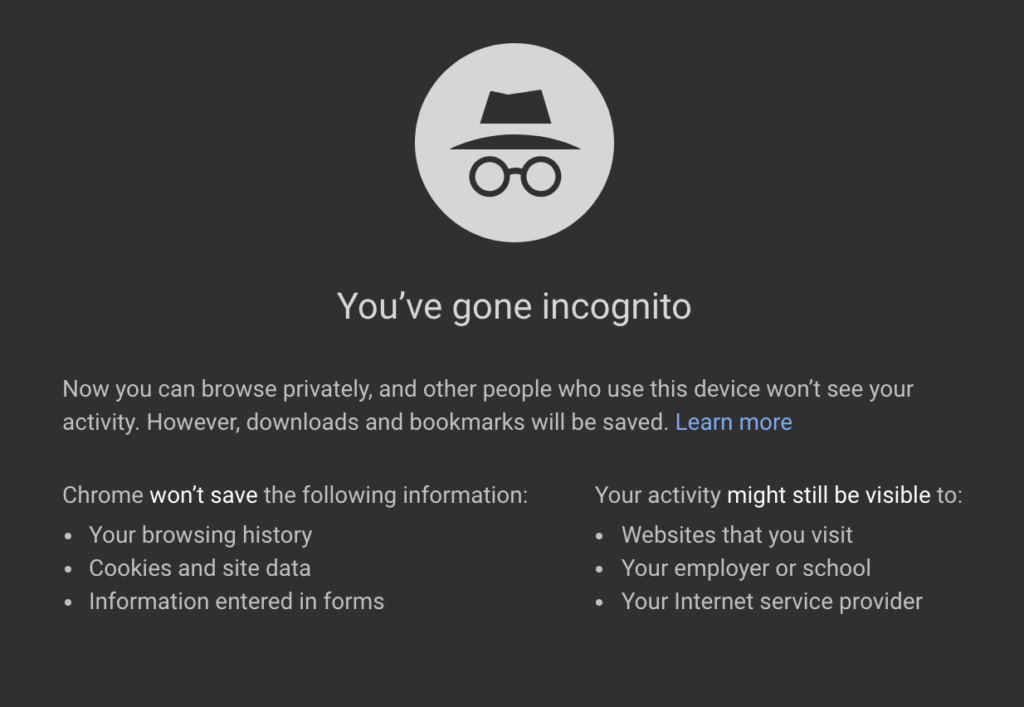
This is one great way to conduct your online actions without being caught or trapped. The great thing with incognito modes is they can be done anytime when you want to access the online world with a browser without the fear of the history being saved and cookies to interrupt.
2 . PLUGINS
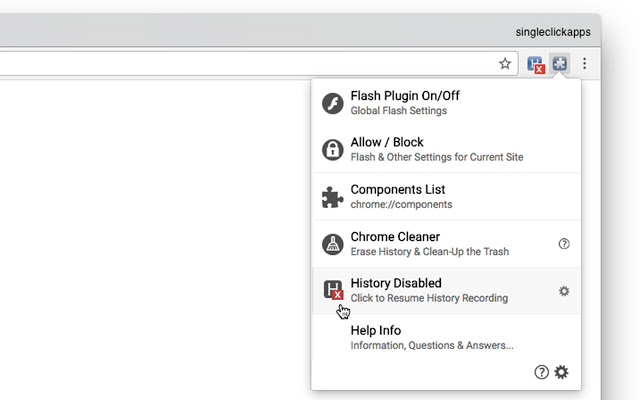
There are multiple plugins that you can make use of so that you're not being tracked online. Reliable ones are AdblockPlus, Disconnect, and more. They are framed in such a manner where the scripts are directly blocked wherein ads and trackers come into contact with you.
3. ELIMINATE FLASH AND JAVASCRIPT
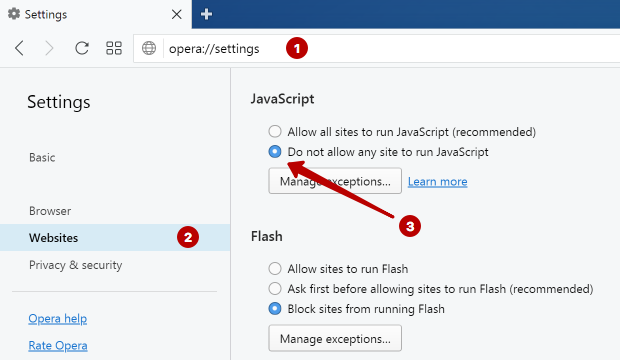
Another great way to eliminate your fingerprints online is to eliminate Flash and Javascript. These two are factors where no detection of fonts, cookies, and more will be available. However, there can be a reduced performance in your online actions but the security will be great.
4. INVEST IN ANTI-MALWARE SOFTWARES
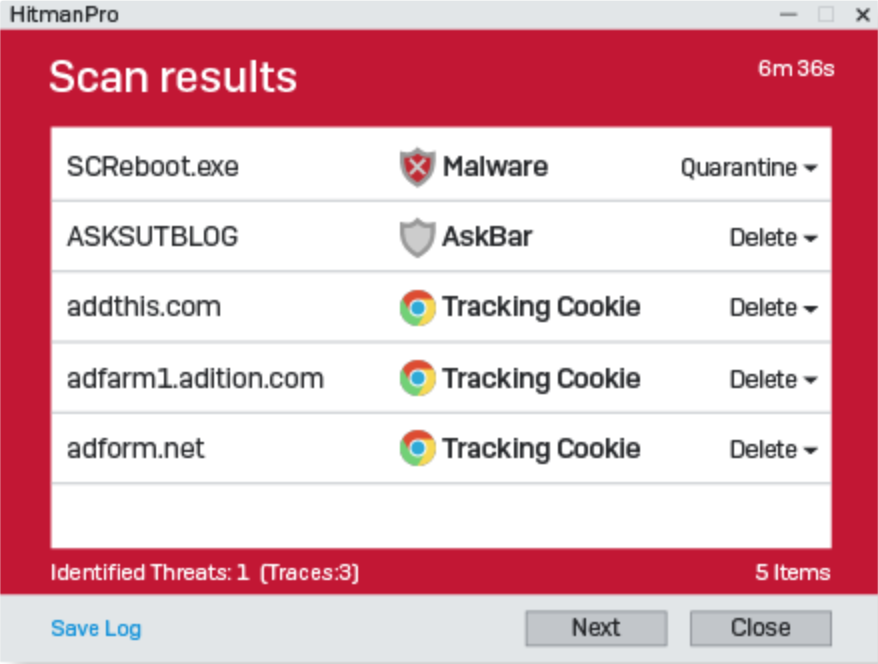
Another great way to eliminate your online fingerprinting is to invest in anti-malware softwares. They are great to secure your online actions as well as guard your device and other private information. You can get started with these Malwarebytes and HitmanPro as they are considered to be the best malware tools present.
5. MAKE USE OF THE TOR BROWSER
Another way to eliminate your online fingerprinting actions is by using the tor browser or also called The Onion Router. The Tor browser can be accessed with a great VPN service for a better impact. It does a great job of blocking Javascript codes on websites and also makes it difficult for any hacker to try and capture your browser fingerprints.
6. USE A PROXY SERVER
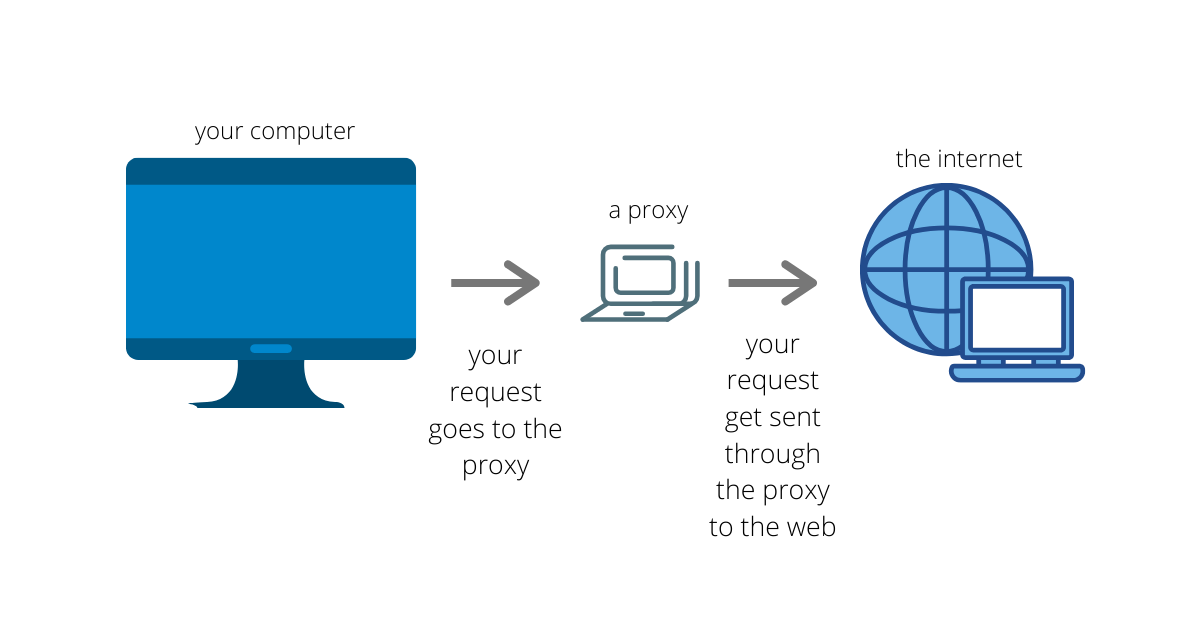
Making use of a reliable proxy server does a great job in ensuring that one thing, your IP doesn’t give your details away and secondly, your online actions are secured.
A proxy server is a solution that helps you a brand to access any kind of information from any source without the fear of their identity being hidden. For instance, say you want to access information from your competitors in order to understand what their particular strategies are. The first step you would do is to send a request to view their website.
Instead of the request reaching their website, the proxy server will receive it first. The proxy server will change your IP address and then send the request. Once your competitors approve of the request sent, you can then access their information.
Interesting Read : [**The Ultimate Dedicated Proxy Guide [2020]**](https://limeproxies.com/blog/ultimate-dedicated-proxy-guide-2020/)
For instance, now your competitors have only limited their data access on their website to certain users. If you are not a part of those set users, chances are you would either have the request denied or be blocked. The way they find out is through the IP address you hold.
What a proxy server does is it hides your IP address and showcases another IP address so when your competitors receive it, they will think that you are a part of their users and give you access. When this action is being conducted, proxy servers ensure that nowhere at any point will your identity be revealed.

About the author
Rachael Chapman
A Complete Gamer and a Tech Geek. Brings out all her thoughts and Love in Writing Techie Blogs.
Related Articles
How to Scrape Competitive Pricing with Proxies
One of the goals of scraping is to give you an edge over the competition in the market. Know how to Scrape Competitive Pricing with Proxies
The Role of Clean Data Sets in AI and ML to Drive Meaningful ROI
Data has become an important part of businesses as many decisions bank on collected and analyzed data. Learn Here More on The Role of Clean Data Sets in AI and ML to Drive Meaningful ROI.